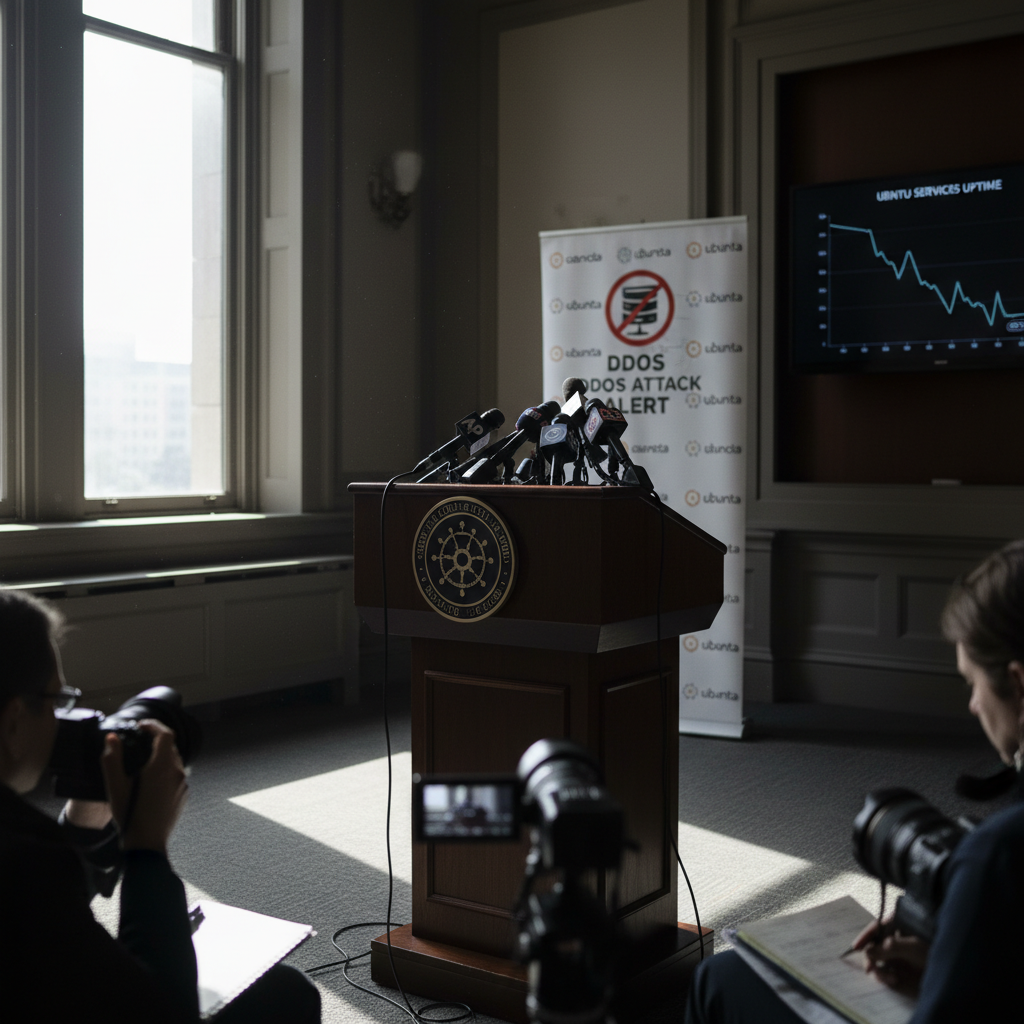
Canonical Confirms DDoS Attack Knocked Ubuntu Services Offline for Nearly a Day
Zero Signal Staff
Published May 1, 2026 at 12:03 PM ET · 11 hours ago
TechCrunch, The Register, OMG! Ubuntu, Canonical
A sustained distributed denial-of-service attack disrupted Ubuntu and Canonical web services for roughly 20 hours beginning Thursday, the company confirmed, knocking out key developer tools including Launchpad, Livepatch, and login infrastructure.
A sustained distributed denial-of-service attack disrupted Ubuntu and Canonical web services for roughly 20 hours beginning Thursday, the company confirmed, knocking out key developer tools including Launchpad, Livepatch, and login infrastructure. A group calling itself The Islamic Cyber Resistance in Iraq, also known as 313 Team, claimed responsibility on Telegram and followed the claim with what The Register described as an extortion-style message to Canonical.
The Details
Canonical posted an official statement on May 1 acknowledging the attack. "Canonical's web infrastructure is under a sustained, cross-border attack and we are working to address it," the company said. A Canonical spokesperson separately confirmed to The Register that the disruption was a distributed denial-of-service attack, adding that the company was working to restore full availability to affected services.
According to OMG! Ubuntu, the affected properties included ubuntu.com-linked services such as Launchpad, Livepatch API, Landscape, login.ubuntu.com, security.ubuntu.com, and archive.ubuntu.com, along with several Canonical subdomain services. OMG! Ubuntu reported that mirrored APT repositories and OS images remained available through distributed infrastructure even as the core services went down.
TechCrunch reported that developers discussing the incident said Ubuntu's security API and several Ubuntu and Canonical websites were affected. TechCrunch said it verified the impact directly, noting that package updates failed on a test Ubuntu device during the outage.
There is a partial discrepancy in how sources characterized the package-update disruption. OMG! Ubuntu reported that mirrored APT repositories were not fully offline, while TechCrunch's testing showed update failures on at least one device. The difference likely reflects uneven impact across mirrored services and endpoints depending on which server a user's system was pointed to.
The Register reported that some properties, including Archive and Discourse pages, remained reachable even while Ubuntu's main website and other services were disrupted — consistent with the picture of partial, uneven availability across Canonical's infrastructure.
The Register attributed the responsibility claim to a group calling itself The Islamic Cyber Resistance in Iraq, also known as 313 Team, which posted to Telegram. The outlet reported the group followed up with an extortion-style message directed at Canonical. Canonical had not publicly responded to or verified the attribution claim at the time of reporting.
Context
TechCrunch reported that the outage had lasted roughly 20 hours at the time of its publication, placing the start of disruption on Thursday. Canonical's spokesperson statement to The Register — confirming the attack as a DDoS — was among the clearest official disclosures the company made during the incident, though the company had not published a full technical postmortem or a complete list of affected services as of the time of reporting.
The affected infrastructure spans tools that are integral to many Ubuntu-based workflows. Launchpad is the primary platform Canonical uses for package management, bug tracking, and code hosting. Livepatch allows security patches to be applied to running Linux kernels without requiring a reboot — a service relied on by system administrators prioritizing uptime. Login and security infrastructure sit at the center of identity and update verification for Ubuntu users and enterprise customers.
The 313 Team attribution, as reported by The Register, was based on self-identification by the group on Telegram and was not independently verified by Canonical. The Register also described a subsequent extortion-style message sent to the company, though the nature or specific demands of that message were not detailed in published reporting.
What's Next
Canonical had not published a full technical postmortem or a complete affected-service list at the time of research, according to the fact brief. The company said it was working to restore full availability to affected services, per its spokesperson statement to The Register, but no timeline for full restoration was specified in available reporting.
The 313 Team's responsibility claim remains unverified by Canonical as of the time of publication. No details about any response to the reported extortion-style message or law enforcement involvement were available in published reports.
Never Miss a Signal
Get the latest breaking news and daily briefings from Zero Signal News directly to your inbox.
